Reliance solely on the first traditional authentication factor, “what you know,” is often referred to as Single-Factor Authentication, and most commonly requires the user to provide a username and password. In and of itself, the username has limited value in authenticating a user; rather, it serves to identify which user is being presented to a company for authentication. 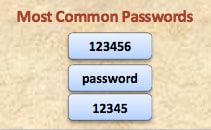

Sources
- See Jordan Crook, This List Of 2014’s Worst Passwords, Including ‘123456,’ Is Embarrassing, TechCrunch (Jan. 20, 2015), http://techcrunch.com/2015/01/20/this-list-of-2014s-worst-passwords-including-123456-is-embarrassing/; see also Chenda Ngak, The 25 most common passwords of 2013, CBSNews.com (Jan. 21, 2014), http://www.cbsnews.com/news/the-25-most-common-passwords-of-2013/.
- See, e.g., NIST, DEP’T OF COMMERCE, SPECIAL PUBL’N NO. 800-63-2, GUIDE TO ENTERPRISE PASSWORD MANAGEMENT (DRAFT) 3-8 (Aug. 2009), http://csrc.nist.gov/publications/drafts/800-118/draft-sp800-118.pdf [hereinafter NIST Password Management] (“It is generally unrealistic to expect users to memorize [long, automatically generated] passwords. For passwords that are intended to be memorized, organizations should consider security needs and expected user behavior when deciding which password generation method should be used.”).
- See Internal Revenue Service, Dep’t of the Treasury, Safeguards Technical Assistance Memorandum: Multi-Factor Authentication Implementation (June 2013), http://www.irs.gov/file_source/pub/irs-utl/safeguards-multi-factor-auth-alert.doc (“One type of authentication may not be repeated in attempting to satisfy Multi-Factor Authentication. For example, authenticating using two passwords does not constitute multi-factor. They are both part of ‘Something you know’ and can both only satisfy this category.”).