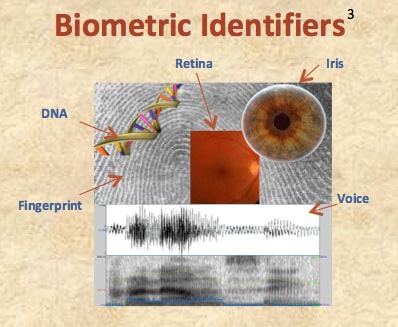
Some authentication systems employ a third factor—“what you are.” Implementation of this third factor typically involves use of Biometrics (e.g., voiceprints, fingerprints, iris patterns, retinal patterns, DNA).1 The use of Biometrics for authentication is based on the presumption that each individual has certain biological characteristics that permit unique identification of that individual.
While the use of Biometrics is generally believed to offer a high level of security, the security provided by any given biometric measure may depend in part on how the measure is implemented, which may, in turn, raise issues of user convenience. Thus, for example, there is an Error-Rate Tradeoff associated with biometric authentication, under which an increase in security is “almost universally” correlated to an increase in the False Rejection Rate—that is, the percentage of legitimate users who are not permitted to access the system.2
Sources
- See, e.g., NIST, DEP’T OF COMMERCE, SPECIAL PUBL’N NO. 800-63-2, ELECTRONIC AUTHENTICATION GUIDELINE 20 (Aug. 2013), http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-63-2.pdf.
- See, e.g., NIST, DEP’T OF COMMERCE, SPECIAL PUBL’N NO. 800-76-2, BIOMETRIC SPECIFICATIONS FOR PERSONAL IDENTITY VERIFICATION, at n. 26 and accompanying text (Jul. 2013), http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-76-2.pdf (“High false rejection rates will inconvenience legitimate users, and it is therefore imperative that biometric systems offering sufficient performance are used.”).
- Image sources: Voice — http://commons.wikimedia.org/wiki/Category:Voice_spectrograms#mediaviewer/File: Pronouncing.PNG; Fingerprint — http://commons.wikimedia.org/wiki/File:Fingerprint_Whorl.jpg; Retina — http://commons.wikimedia.org/wiki/File:Human_eye1.jpg; Iris — http://commons.wikimedia.org/wiki/File: Iris.eye.225px.jpg; DNA — http://upload.wikimedia.org/wikipedia/commons/9/97/DNA_Double_Helix.png.